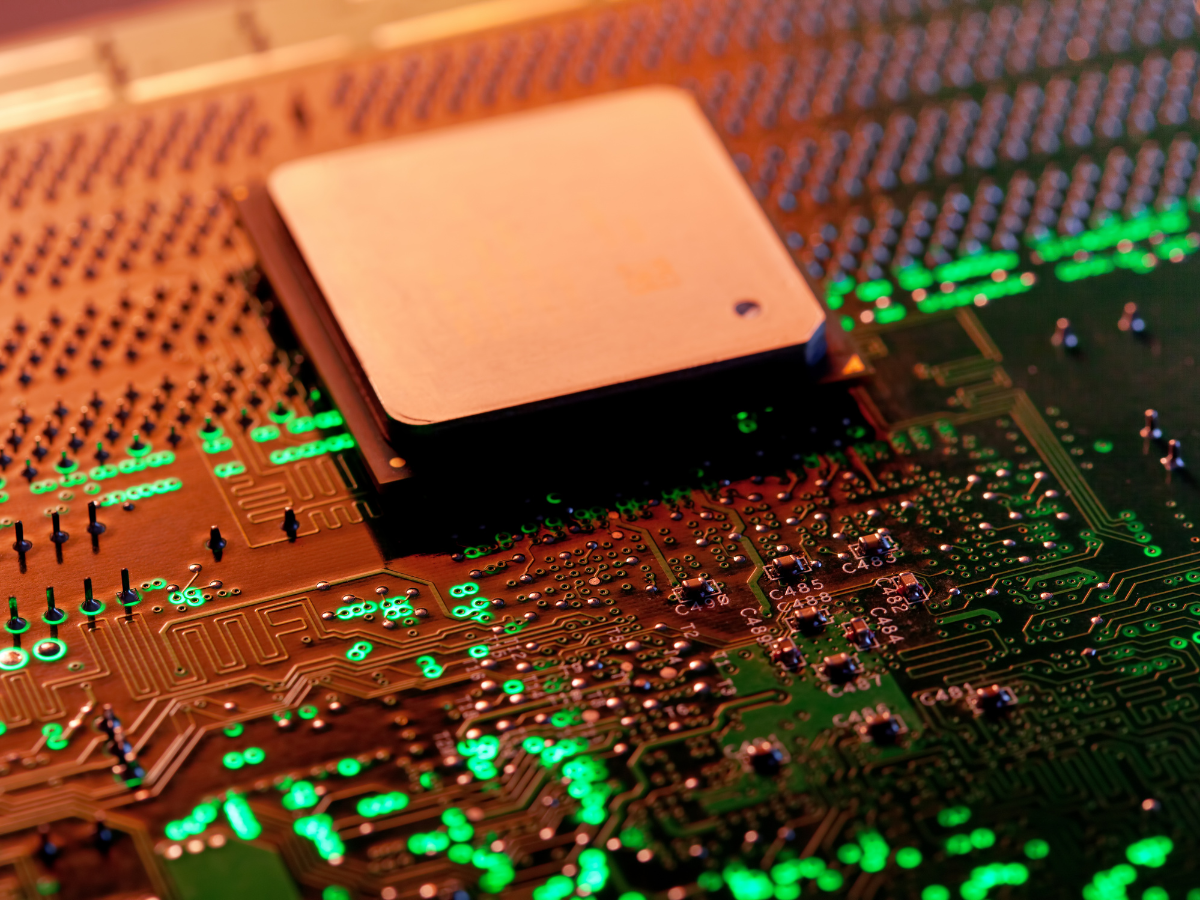
A team of academic researchers has recently disclosed browser-based and timerless speculative execution attacks on Apple devices. This side channel attack exploits a weakness in the A and M series CPUs running on Apple iOS, iPadOS and macOS devices. The attack vector named iLeakage is able to extract sensitive personal information of Apple users by exploiting the Safari web browser.
“An attacker can induce Safari to render an arbitrary webpage, subsequently recovering sensitive information present within it using speculative execution,” researchers Jason Kim, Stephan van Schaik, Daniel Genkin, and Yuval Yarom said in a new study.
In a practical attack scenario, the attacker baits the targeted Safari user to a malicious website. The malicious website then automatically opens the site that the user intended to visit. iLeakage can do this because its rendering process handles both the attack website and the targeted site simultaneously.
Experts have already demonstrated how iLeakage could be used to obtain passwords as well as other sensitive information. Here are the video demos that show exactly how the attack vector works
- Stealing Instagram credentials that are auto-filled by a password manager
- Extracting email subject lines from a Gmail inbox
- Recognizing users’ YouTube watch history
As per Apple store’s policy, all third-party browsers must use Safari’s WebKit engine. This implies that browsers like Chrome or Firefox are essentially Safari with proprietary user interface and wrapping. Therefore, all browsers in your Apple device (except macOS) are equally susceptible to this attack vector.
Report findings were sent to Apple back in September 2022 pinpointing the shortcomings in all Apple devices powered by Apple’s A-series and M-series ARM processors released in 2020 and onward. However, the tech giant seemingly addressed a mitigation tool for Safari on macOS only. They have a plan to further address the issue in their next scheduled software release.
Shedding light on the iLeakage work mechanism
iLeakage works similarly to the two most famous side-channel attacks (SCAs) Meltdown and Spectre. Apple’s chip works in a speculative execution model and that’s the glitch iLeakage exploits. In fact, most modern CPUs follow the same model to give users a faster and seamless experience.
In the speculative model, CPUs predict a task will be ordered before the user puts an actual command. In a bid to create a faster experience, the CPU completes the first part of the task that it predicted. If the task is not eventually asked by the user, the CPU reverts to the original state by erasing the pre-executions.
This is where the attack vector outsmarts a CPU. It manipulates CPUs into pre-executing incorrect instructions that depend on sensitive data. This data is then gathered through a side channel even after the CPU realizes its mistake.
To wrap things up
Researchers are yet to gather evidence of iLeakage causing havoc as the attack is not easy to conduct. “It requires advanced knowledge of browser-based side-channel attacks and Safari’s implementation,” the researchers said.
On the flip side, the attack would be very difficult to detect if it is launched on a massive scale since it runs in Safari and never leaves a trail in system log files. “iLeakage shows that the Spectre attack is still relevant and exploitable, even after nearly 6 years of effort to mitigate it since its discovery,” the researchers noted.